SaaS platforms now support a wide range of healthcare operations, from patient communication and scheduling to records access, billing workflows, analytics, and telehealth experiences. That creates opportunity, but it also creates serious compliance obligations when protected health information is involved.
If your software stores, processes, transmits, or helps manage health-related data for healthcare organizations, HIPAA compliance is not something you can treat as a checkbox. It affects product design, infrastructure, access controls, vendor management, internal policies, incident response, and day-to-day operations.
For SaaS companies serving healthcare clients, the real question is not simply, “Are we HIPAA compliant?” The better question is: What specific responsibilities apply to our product, our role, and our handling of PHI?
This guide explains the fundamentals in a practical way.
What HIPAA compliance means for SaaS providers
HIPAA, the Health Insurance Portability and Accountability Act, is a US law that sets standards for protecting sensitive patient health information. For software companies, HIPAA becomes relevant when a platform handles protected health information, often called PHI.
PHI generally refers to individually identifiable health information. This can include patient names, diagnoses, treatment details, appointment data, insurance information, medical record numbers, and other information linked to a person’s health or care.
In practice, HIPAA compliance is not about making a marketing claim. It is about implementing the right legal agreements, technical safeguards, administrative processes, and operational controls to protect that data appropriately.
For most SaaS websites and healthcare applications, this means your compliance position depends on how your product is used, what data it touches, and who you serve.
Why HIPAA matters in SaaS and cloud environments
Healthcare has become increasingly dependent on cloud-based systems. That makes SaaS products more useful, but also more exposed to compliance and security risks.
A common issue is that software teams assume strong security alone is enough. It is not. You can have a well-built platform and still fall short if you do not have the right policies, access management, vendor agreements, workforce training, or breach response procedures in place.
From an implementation standpoint, HIPAA matters because healthcare clients need confidence that your platform can support secure data handling across the full lifecycle of information, including:
- data collection
- storage
- transmission
- user access
- auditing
- retention
- third-party integrations
- incident response
That is why healthcare buyers often ask SaaS vendors about encryption, logging, backup policies, access restrictions, BAAs, subcontractors, and breach procedures before signing a contract.
Are you a covered entity or a business associate?
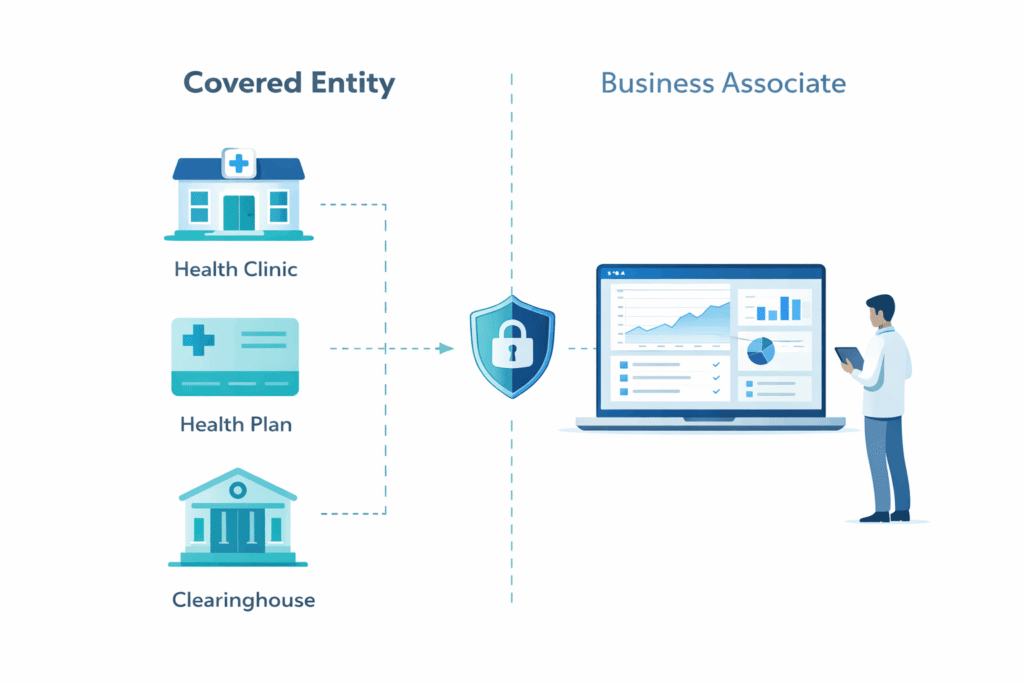
This is one of the first questions a healthcare SaaS company needs to answer.
Covered entity
Covered entities are typically:
- healthcare providers
- health plans
- healthcare clearinghouses
These organizations are directly regulated under HIPAA because they provide care, process claims, or perform covered healthcare functions.
Business associate
A SaaS company is often a business associate if it creates, receives, maintains, or transmits PHI on behalf of a covered entity.
That is the category many healthcare software vendors fall into. If your application hosts patient data, supports care workflows, enables provider communication, or processes information for a healthcare client, you are likely operating as a business associate rather than a covered entity.
One practical way to approach this is to look beyond your brand label. Being a “software company” does not remove HIPAA responsibility if your platform handles PHI for a healthcare organization.
The role of a Business Associate Agreement (BAA)
If you are acting as a business associate, a Business Associate Agreement is usually essential.
A BAA is a contract between the covered entity and the vendor handling PHI. It helps define:
- what PHI is being handled
- why it is being handled
- what safeguards are required
- how breaches must be reported
- what limits apply to use and disclosure
- what responsibilities subcontractors must follow
For SaaS providers, the BAA is not a formality. It is part of the compliance foundation. Without it, a healthcare client may not be able to use your platform for HIPAA-regulated data in a compliant way.
If your SaaS stack relies on other vendors such as cloud hosting, email delivery, support tools, analytics platforms, or backup providers, you may also need to assess whether those vendors handle PHI and whether appropriate downstream agreements are required.
Key HIPAA rules SaaS companies should understand
HIPAA is often discussed as one concept, but in practice it includes several important rules. SaaS teams do not need to become legal scholars, but they do need to understand the basics.
Privacy Rule
The Privacy Rule governs how PHI may be used and disclosed. It focuses on protecting patient information and limiting unnecessary exposure.
For SaaS providers, this matters because product workflows, support practices, and internal access policies should not allow PHI to be used more broadly than necessary.
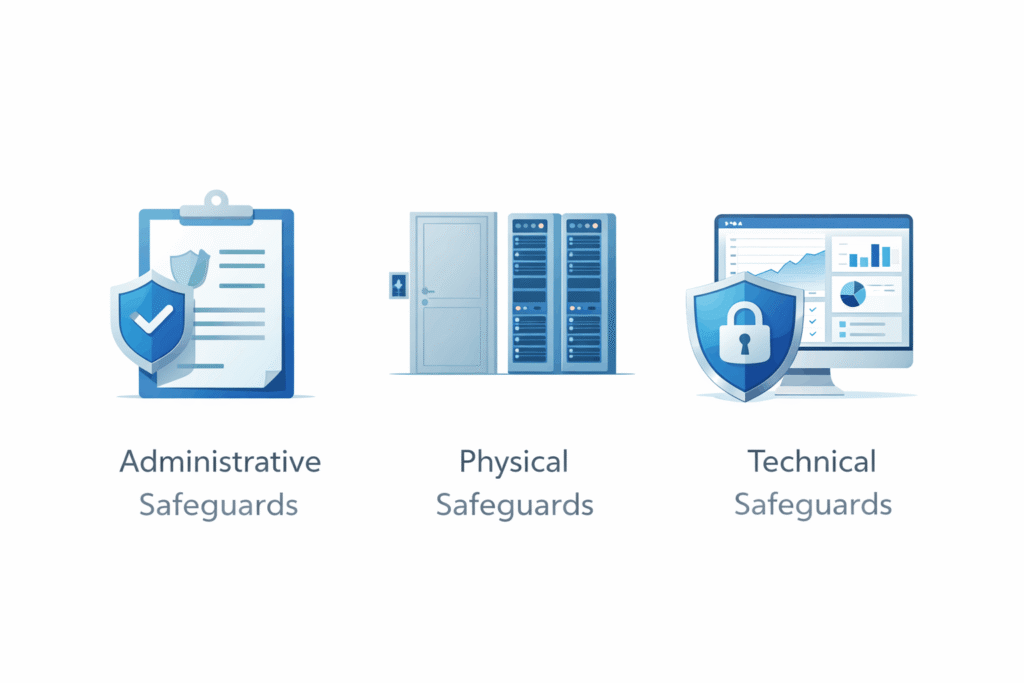
Security Rule
The Security Rule is especially important for digital products because it applies to electronic protected health information, or ePHI.
It requires appropriate administrative, physical, and technical safeguards. This is where issues such as authentication, access controls, audit logs, encryption, device security, and workforce procedures become central.
Breach Notification Rule
If unsecured PHI is breached, HIPAA may require notification to affected parties and regulators within specific timeframes.
For SaaS providers, this means incident detection and response cannot be vague. You need clear escalation procedures, internal responsibilities, documentation practices, and communication workflows.
Enforcement Rule
The Enforcement Rule covers investigations, penalties, and compliance enforcement.
This matters because HIPAA violations can lead to costly consequences, especially when failures involve weak safeguards, repeated noncompliance, or poor breach handling.
Omnibus Rule
The Omnibus Rule strengthened HIPAA requirements in several areas, including business associate accountability.
For SaaS companies, one important takeaway is that vendors handling PHI are not outside the compliance picture. Their obligations are real and should be reflected in operations, contracts, and technical controls.
Core HIPAA compliance requirements for SaaS companies
There is no single technical feature that makes software HIPAA compliant. Compliance comes from a combination of safeguards, processes, and governance.
Here are the areas that matter most.
1. Risk analysis and risk management
A common starting point is a formal risk analysis. This helps identify where PHI enters your systems, how it moves, where it is stored, who can access it, and what could go wrong.
For most websites and applications, risk areas include:
- weak authentication
- poor access separation
- exposed backups
- insecure API connections
- third-party integrations
- overbroad employee access
- insufficient monitoring
- data retention gaps
Risk analysis should lead to actual risk management decisions, not just documentation.
2. Access controls
Not every employee, contractor, or client-side user should have broad visibility into PHI.
Strong access control usually includes:
- role-based permissions
- least-privilege access
- strong password policies
- multi-factor authentication where appropriate
- session security
- restricted admin access
- quick access removal for offboarded users
From an implementation standpoint, access design should be built into the product, not bolted on later.
3. Audit trails and monitoring
Healthcare organizations often need visibility into who accessed information, when they accessed it, and what actions were taken.
Your SaaS platform should support meaningful logging and auditability, especially for sensitive user actions. Logs should be protected, retained appropriately, and usable during investigations or client reviews.
4. Encryption and secure transmission
Encryption is a major part of protecting ePHI, especially in cloud environments.
In practice, this usually means:
- encryption in transit
- encryption at rest where appropriate
- secure key management
- secure file transfer methods
- properly configured databases and storage systems
Encryption alone is not enough, but it is a foundational control for healthcare software.
5. Administrative safeguards
HIPAA is not only about infrastructure. It also requires internal operational discipline.
Administrative safeguards often include:
- documented policies and procedures
- workforce training
- assigned security responsibility
- incident response planning
- access review processes
- vendor oversight
- sanctions for policy violations
A common issue is that fast-growing SaaS companies focus heavily on shipping product and underinvest in policy maturity. That becomes a problem when enterprise healthcare clients start asking deeper compliance questions.
6. Physical safeguards
Even cloud-based SaaS products have physical security considerations, especially around devices, office practices, endpoint usage, and infrastructure relationships.
If you rely on cloud providers, you still need to understand the shared responsibility model. Your infrastructure provider may secure the data center, but your company remains responsible for how your application, accounts, and workflows are configured.
7. Workforce training
HIPAA failures are not always caused by code defects. They often happen because of human error.
Employees should understand:
- what PHI is
- how to handle it safely
- what should never be shared casually
- how to report incidents
- how support and engineering teams should work with sensitive data
This is especially important for customer support, QA, operations, and engineering staff.
8. Breach response readiness
Every SaaS company serving healthcare should have a documented incident response process.
That process should address:
- detection
- containment
- investigation
- internal escalation
- documentation
- client notification steps
- legal and compliance review
- remediation
One practical way to approach this is to prepare for the process before an incident happens. Once a real event occurs, unclear internal ownership creates delays and mistakes.
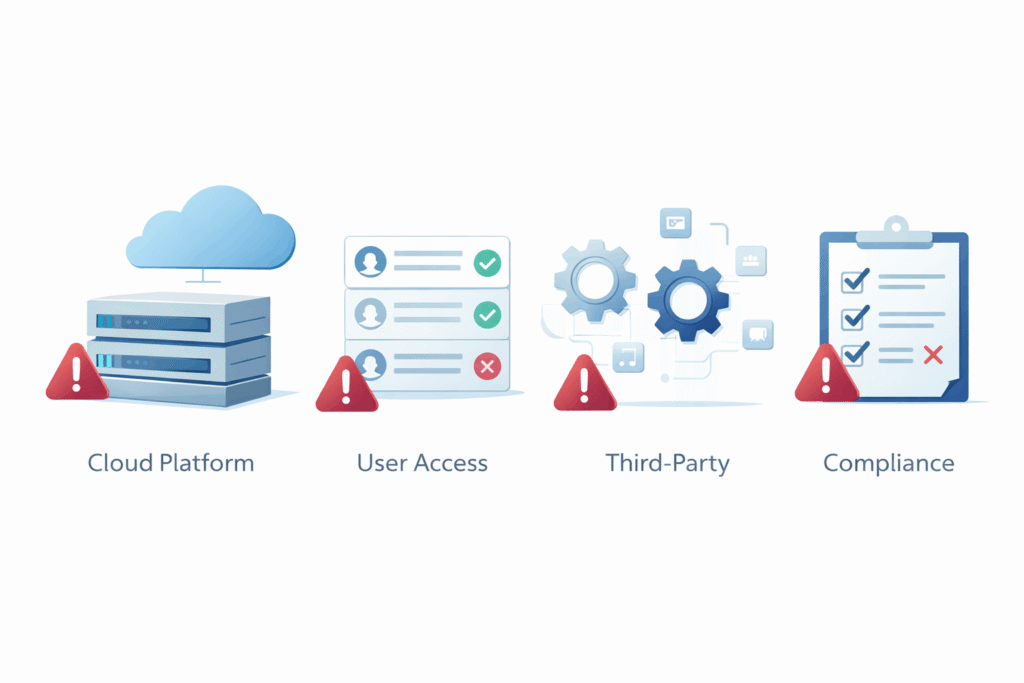
HIPAA compliance in cloud-based SaaS products
Cloud delivery does not remove HIPAA obligations. It changes how they must be managed.
If your healthcare SaaS product runs on cloud infrastructure, you should evaluate:
- where PHI is stored
- which services touch PHI
- which vendors are in scope
- what security settings are enabled
- whether backups and logs contain PHI
- whether support tools and integrations expose sensitive data
For most cloud-based products, the compliance challenge is not only the main application database. It is the broader ecosystem around the product, including monitoring tools, ticketing systems, storage buckets, development workflows, and connected services.
That is why HIPAA readiness usually requires both legal review and technical review.
Can software be advertised as HIPAA compliant?
This area should be handled carefully.
Saying a SaaS platform is “HIPAA compliant” can be oversimplified if it suggests universal certification or blanket approval. HIPAA does not work like a simple badge program for software products.
A more credible approach is to explain that the platform is designed to support HIPAA requirements when configured and used appropriately, and that the provider offers relevant safeguards and a Business Associate Agreement where applicable.
That wording is usually more responsible because compliance depends on both the vendor and the healthcare organization using the system correctly.
Common HIPAA Compliance Mistakes SaaS Companies Still Make
Many healthcare SaaS companies do not fail because they ignore HIPAA completely. More often, they run into trouble because they misunderstand how broad compliance really is. A platform may look secure on the surface, yet still have serious gaps in process, access control, vendor oversight, or incident readiness.
Here are some of the most common mistakes.
Assuming cloud hosting makes the product HIPAA compliant
This is one of the most common misunderstandings in healthcare SaaS.
Using a well-known cloud provider is helpful, but infrastructure alone does not make your application compliant. A secure hosting environment does not automatically cover how your product handles permissions, user activity, logging, support access, internal workflows, backups, or connected tools.
In practice, HIPAA risk often sits at the application and operations layer, not just the server layer. A SaaS company may host on strong infrastructure and still expose PHI through weak admin controls, poor account segmentation, misconfigured storage, or insecure internal processes.
Signing a BAA before the business is actually ready
Some SaaS vendors treat the Business Associate Agreement as a sales document rather than a compliance commitment.
That is risky. Signing a BAA tells the client that your company is prepared to handle protected health information responsibly and within defined obligations. If your internal controls are immature, your documentation is incomplete, or your team has no clear incident response process, that agreement can create serious operational and legal exposure.
One practical way to approach this is to treat the BAA as the result of readiness, not a shortcut to credibility.
Overlooking subcontractors and third-party tools
Many SaaS platforms rely on a wider stack than teams initially realize. PHI exposure may not happen only inside the core application. It can also appear in monitoring tools, support platforms, email systems, file-sharing workflows, analytics products, backup services, and communication tools.
A common issue is that companies focus heavily on their main product database while ignoring the broader vendor ecosystem around it. If a third-party service can access, store, transmit, or surface PHI, it needs to be reviewed carefully from both a security and compliance standpoint.
From an implementation standpoint, vendor management should be part of HIPAA planning from the start, not something reviewed only after procurement questions arise.
Giving internal teams broader access than they need
Not every employee needs access to production data, and not every technical workflow justifies visibility into PHI.
This often becomes a problem in fast-moving SaaS environments where engineers, QA teams, support staff, contractors, or temporary team members are given broad access for convenience. Over time, that creates unnecessary exposure and weakens the principle of least privilege.
For most healthcare software products, access should be limited by role, reviewed regularly, and removed quickly when responsibilities change. Strong compliance is not only about keeping outsiders out. It is also about controlling unnecessary internal access.
Treating HIPAA as a one-time setup instead of an ongoing discipline
Another mistake is assuming that once policies are written and a few controls are in place, the work is done.
HIPAA compliance is not static. Products evolve. New features are released. Vendors change. Teams grow. Integrations expand. Infrastructure is updated. Each of those changes can introduce new compliance considerations.
For most websites and SaaS products in healthcare, the better approach is continuous review. Risk analysis, access policies, training, logging, vendor oversight, and incident response should be revisited as the business changes. A compliance posture that worked a year ago may no longer match how the platform operates today.
Focusing on policy language while ignoring day-to-day execution
Some companies invest in polished documentation but fall short in real-world implementation. They may have written policies for access control, incident handling, or employee training, but the actual workflows do not reflect those policies consistently.
That gap matters. Compliance is tested in practice, not just on paper. If support teams handle customer issues informally, if offboarding is delayed, or if audit logs are not reviewed meaningfully, written policies alone offer limited protection.
A practical way to approach HIPAA readiness
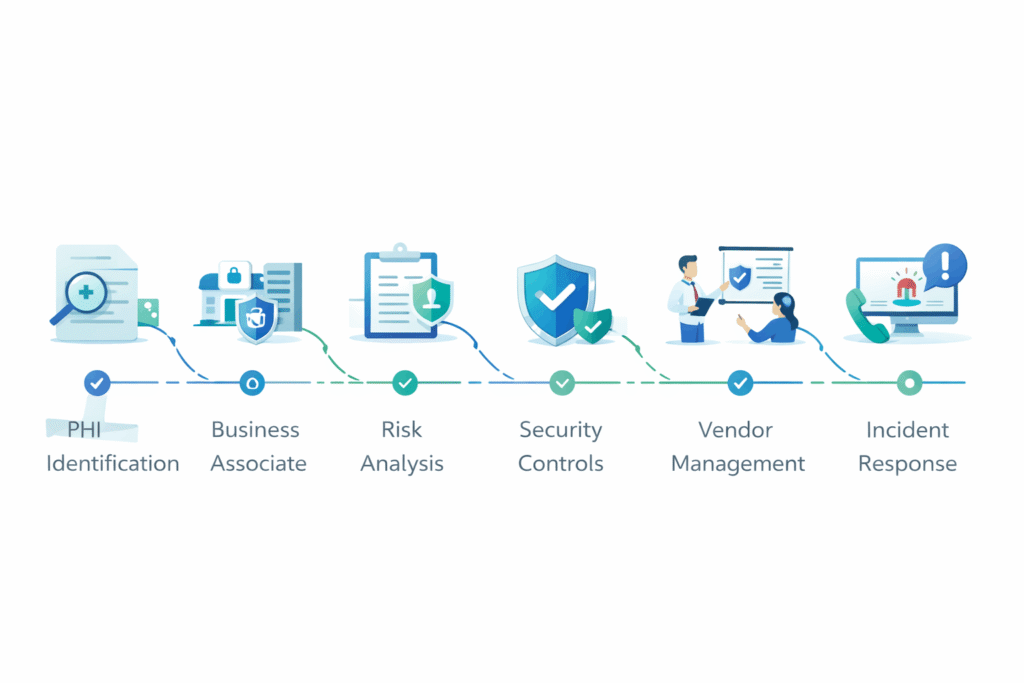
If you are building or growing a SaaS product for healthcare, a practical compliance path often looks like this:
- Identify whether your platform handles PHI.
- Determine whether you are acting as a business associate.
- Map where PHI is collected, stored, processed, and shared.
- Review vendor relationships and downstream exposure.
- Conduct a risk analysis.
- Strengthen technical, administrative, and access safeguards.
- Prepare or review your BAA process.
- Document policies, training, and incident response.
- Reassess regularly as the product evolves.
For most SaaS businesses, this work is easier and less expensive when started early. Retrofitting compliance into a mature product is usually more difficult than designing with compliance in mind from the beginning.
Why this matters beyond compliance
HIPAA is often discussed in legal terms, but it also affects trust, sales, retention, and market credibility.
Healthcare buyers want evidence that a software partner understands the sensitivity of the data involved. A mature compliance posture can support smoother procurement, stronger enterprise conversations, and fewer objections during vendor review.
In other words, HIPAA readiness is not only about avoiding penalties. It is also part of building a serious healthcare SaaS business.
Final thoughts
For SaaS companies working with healthcare organizations, HIPAA compliance is not optional when protected health information is involved. The key is understanding your role, knowing whether you function as a business associate, and building the right mix of legal, technical, and operational safeguards around your product.
The strongest approach is practical rather than promotional. Know what data you handle. Understand your obligations. Review your vendors. Build secure systems. Train your team. Document your processes. Revisit your controls as the platform grows.
That is what turns HIPAA from a vague requirement into an operational standard your business can actually support.
FAQs:
1. What is HIPAA compliance in SaaS?
HIPAA compliance in SaaS means a cloud software provider has the necessary safeguards, policies, and contractual processes in place to support the secure handling of protected health information for healthcare-related use cases.
2. Is every healthcare SaaS company a business associate?
Not automatically. A SaaS company is usually a business associate when it creates, receives, maintains, or transmits PHI on behalf of a covered entity. The exact role depends on how the software is used and what data it handles.
3. Does signing a BAA make software HIPAA compliant?
No. A BAA is important, but it is only one part of compliance. The company still needs appropriate security controls, policies, workforce training, risk management, and breach response procedures.
4. Can cloud-hosted software be HIPAA compliant?
Yes, cloud-hosted software can support HIPAA requirements, but only if the platform, vendor relationships, and internal processes are designed and managed appropriately. Hosting in the cloud alone does not make a product compliant.
5. What security features are most important for HIPAA-ready software?
Key areas include access controls, audit logs, encryption, secure transmission, role-based permissions, incident response planning, workforce training, and ongoing risk assessment.
6. Can a SaaS company say it is HIPAA compliant on its website?
It can, but the wording should be careful and accurate. A more credible approach is to explain that the platform is designed to support HIPAA requirements when properly configured and used, rather than presenting compliance as a simplistic badge.
7. What is the difference between PHI and ePHI?
PHI is protected health information in any form. ePHI refers specifically to electronic protected health information that is created, stored, transmitted, or processed digitally.
8. How often should a SaaS company review HIPAA compliance controls?
Regularly. Reviews should happen whenever there are major product, infrastructure, staffing, or vendor changes, and as part of an ongoing compliance and risk management process.



